-
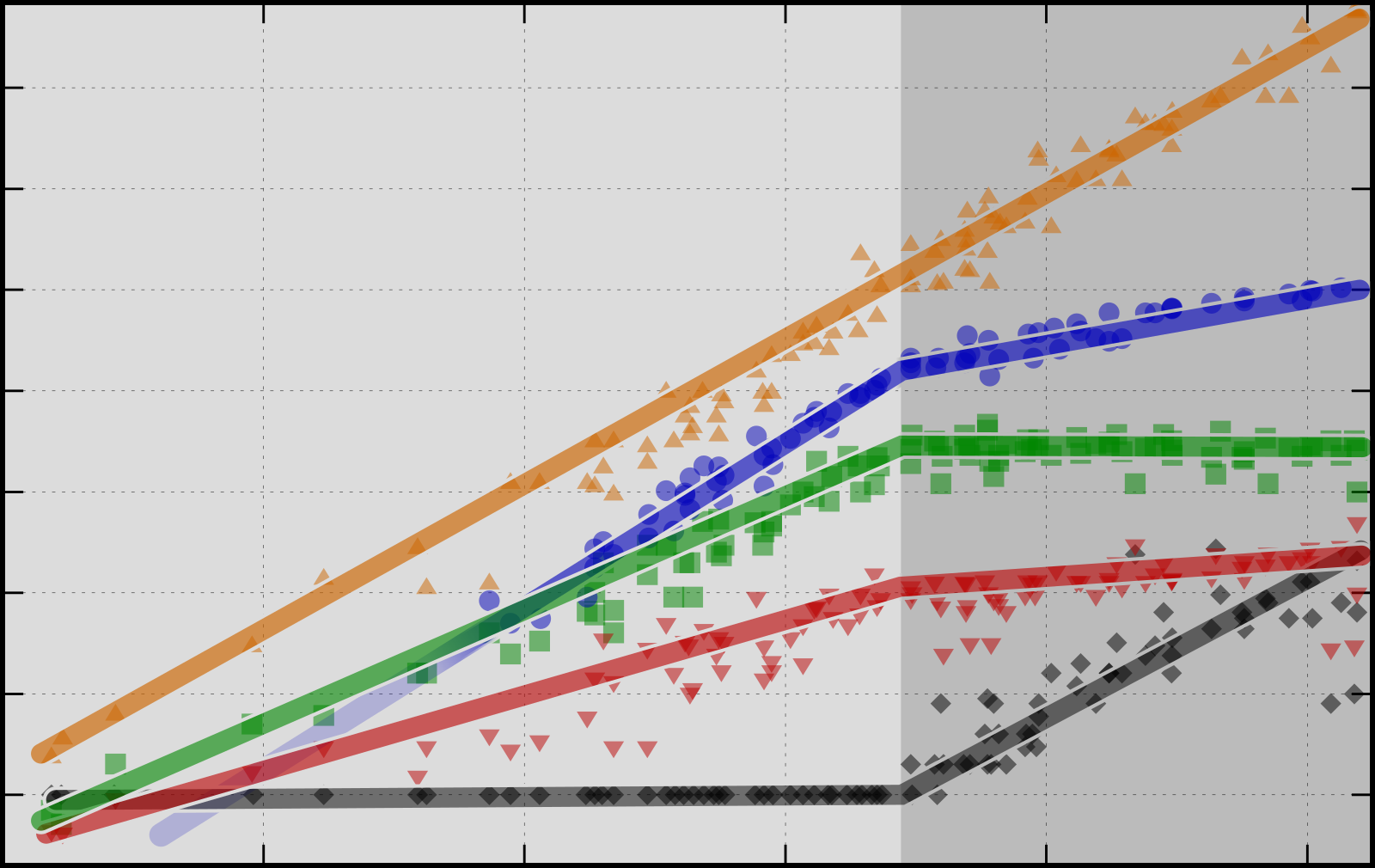
50 years of microprocessor trend data
-
Counting like a computer

-
The year in review

-
Post Quantum and Homomorphic Encryption made easy
Major challenges in computer and information security are the advent of quantum computers and the need to trust your data to (cloud) service providers. New cryptography is supposed to help, but they look daunting. At their core, however, they are just children’s riddles. An introduction to Lattice cryptography and Learning With Errors.
-
Web3 is just expensive P2P
-
Telephony of Everything: From IoT to ToE

-
Ransomware is different



