-
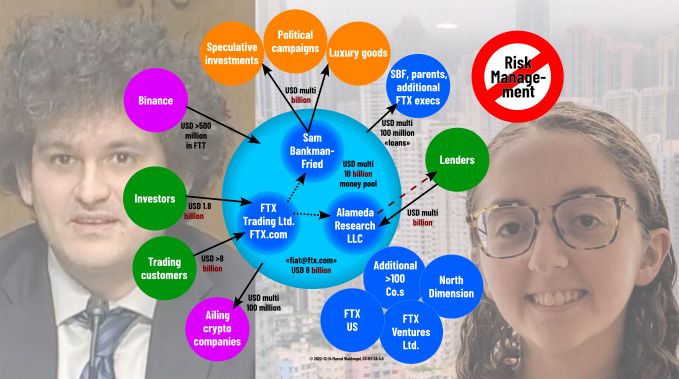
The FTX crypto exchange and its spider web
-
Reproducible AI Image Generation: Experiment Follow-Up
-
Web3 for data preservation? (Or is it just another expensive P2P?)
-
«The Cloud» does not exist
What is cloud anyway? And why are not all clouds the same? An overview to create clarity. The topic of the cloud is currently on everyone’s lips again, and decisions are pending in many places. Clarity is essential for assessing the impact on individuals, the economy and society. That’s why we’re starting a small series…
-
What is an NFT, behind the scenes?
“NFT” is currently on everyone’s lips again, and not only because of Pro Senectute. But what is actually behind the full-bodied promises of the NFT advocates? For more insights on NFTs and the entire blockchain ecosystem, click here. You can also read this text in German 🇩🇪. “NFT” stands for “Non-Fungible Token” and is being…
-
Offline digital cash?
-
The NFT Danger Zone

-
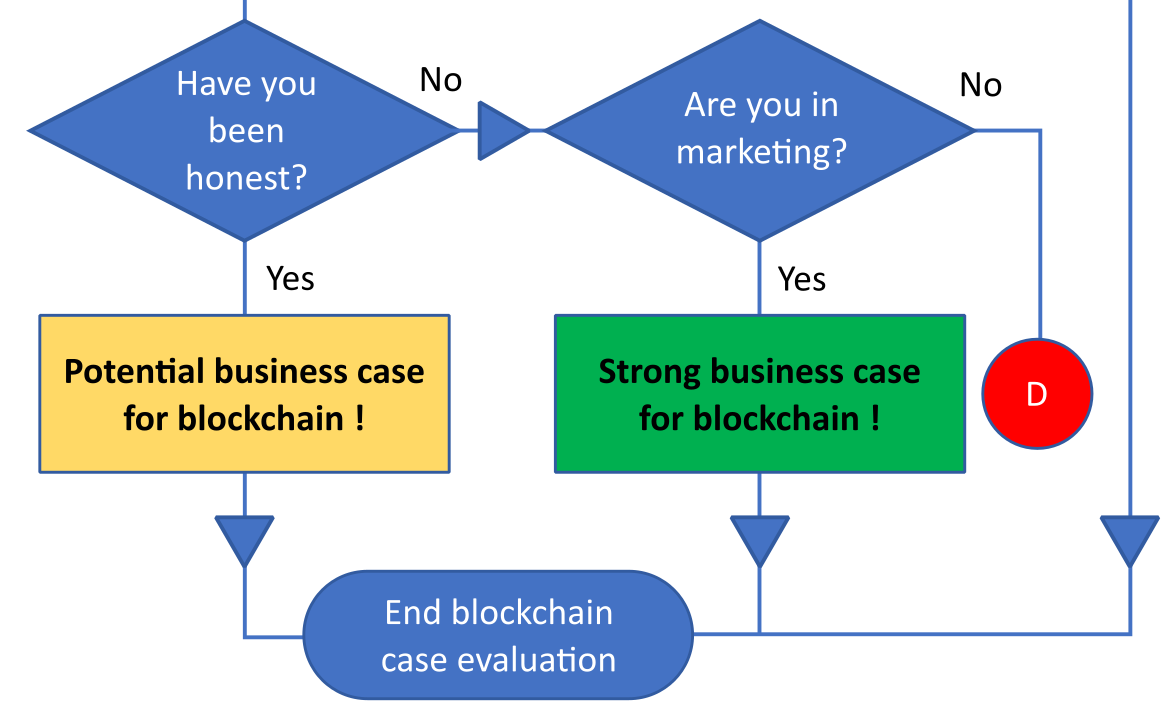
A business-driven blockchain evaluation flow chart
-
Blockchain in a nutshell