Abstract
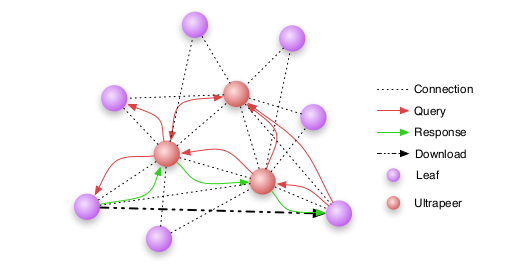
Since the advent of P2P networks they have grown to be the biggest source of internet traffic, superseding HTTP and FTP. For service providers P2P traffic results in increased costs for both infrastructure and transportation. Interest is high to reliably identify the type of service to ensure quality of service. In this document we analyze P2P network architectures and give an overview of existing identification mechanisms. In addition we devise a simple identification scheme suitable for implementation in resources restricted environments with limited computational power and memory. The scheme is based on behavior analysis and as such is not prone to traffic obfuscation techniques.
BibTeX (Download)
@techreport{Zink2010Analysis,
title = {Analysis and Efficient Classification of P2P File Sharing Traffic},
author = {Thomas Zink and Marcel Waldvogel},
url = {https://netfuture.ch/wp-content/uploads/2015/02/zink2010analysis.pdf},
year = {2010},
date = {2010-10-01},
urldate = {1000-01-01},
number = {KN-2010-DISY-02},
address = {Konstanz, Germany},
institution = {University of Konstanz},
abstract = {Since the advent of P2P networks they have grown to be the biggest source of internet traffic, superseding HTTP and FTP. For service providers P2P traffic results in increased costs for both infrastructure and transportation. Interest is high to reliably identify the type of service to ensure quality of service. In this document we analyze P2P network architectures and give an overview of existing identification mechanisms. In addition we devise a simple identification scheme suitable for implementation in resources restricted environments with limited computational power and memory. The scheme is based on behavior analysis and as such is not prone to traffic obfuscation techniques.},
keywords = {Peer-to-Peer, Security, Traffic Engineering},
pubstate = {published},
tppubtype = {techreport}
}