-
The dangers of free cloud-based storage
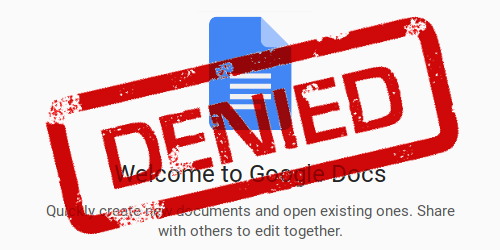
A few days ago, Google Docs locked out many users from their documents, claiming they violated their Terms of Service, despite being innocuous. Here is why this will continue to happen what you can do to not run into this problem yourself.
-
Public NTS Server List

NTS (Network Time Security) is to NTP (Network Time Protocol) essentially what HTTPS is to HTTP: It provides authenticity of the information. Unlike HTTPS, NTS does not provide any confidentiality, as the current time is public information. Want to learn more about NTS? Here is an overview over my NTS articles. NTS Servers Currently, the…
-
How to create DNSsec DANE TLSA entries
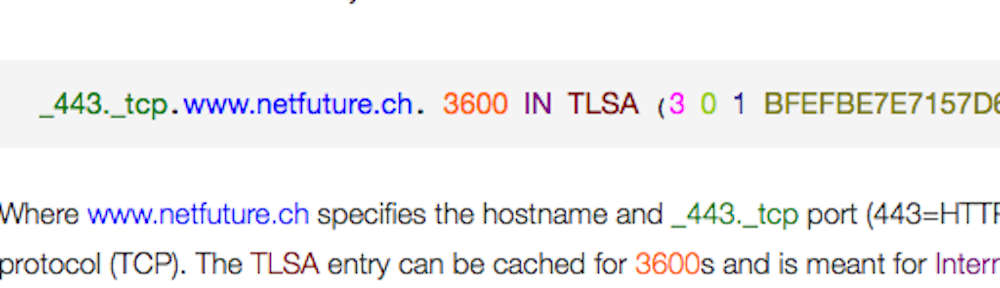
Rationale One of the most promising features for DNSsec is the ability to tell a client which certificate to expect when connecting via Transport Layer Security (TLS). RFC 6698 specifies how TLS Authentication information can be put into DNSsec. So when you ask for the IP address of the server, you can simultaneously obtain the information which…
-
How to block AI crawlers with robots.txt

If you wanted your web page excluded from being crawled or indexed by search engines and other robots, robots.txt was your tool of choice, with some additional stuff like <meta name=”robots” value=”noindex” /> or <a href=”…” rel=”nofollow”> sprinkled in. It is getting more complicated with AI crawlers. Let’s have a look.
-
Weak Keys in RC4
This is an archive of the original posts Andrew Roos made in 1995 to announce his discovery of weak keys in RC4. Even though most Wireless LAN access points avoid these keys since many years, this discovery eventually led to abandoning RC4 for use in WEP (“Wired Equivalent Privacy”) for Wi-Fi networks, as the privacy…
-
Checksums
[simple_series title=”CRC Tutorial”] While parity is adequate to protect a single character or byte, its detection capabilities lack in power when applied to larger messages: Messages often span thousands of bits, and if just two bits are flipped, the corruption will not be detectable. And the chance of having multiple bit errors within a message…
-
Software CRC Computation
[simple_series title=”CRC Tutorial”] /* Created with crc4tab[i] = crc(i); */ char crc4tab = { /* 0:*/ 0, 3, 6, 5, /* 4:*/12, 15, 10, 9, /* 8:*/11, 8, 13, 14, /*12:*/ 7, 4, 1, 2}; int nibble, sum = 0; /* getNextNibble() also needs to return a placeholder for the CRC when sending */ while…